Работа со сканером (поиск вредоносных файлов)
Сканер предназначен для поиска вредоносного кода и файлов, таких как webshell, спамеры и т.д. по базе сигнатур известных нам кодов. Сканер не гарантирует нахождение вируса, а найденный вредоносный файл не обязательно является вирусом. Каждый результат необходимо анализировать и проверять.
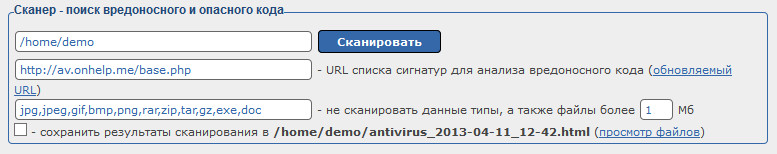
Вы можете выбрать путь для проверки файлов, либо проверить весь хостинг аккаунт, для этого необходимо указать путь — корень аккаунта (/home/логин от хостинга).
Далее укажите ссылку на базы сигнатур. Советуем использовать регулярно обновляемую базу, для этого нажмите на кнопку обновляемый URL.
Ниже указываются форматы файлов для исключения — которые не будут проверяться сканером. Если у вас торрент сайт, то также необходимо добавить формат torrent.
Устанавливая галочку сохранить результаты сканирования, вы сохраните результат в файл, который будет создан в корне хостинг-аккаунта. Используется в том случае, если у вас на хостинге много файлов (от 100 000 файлов).
Результат сканирования
После проверки аккаунта сканером, мы можем увидеть неприятный результат (на скрине приведен пример).
Важно
В первую очередь необходимо обращать внимание на категории сканера Критические файлы и большие закодированные файлы. Во всех остальных категориях указаны файлы с функциями, которые часто используют вредоносные файлы.
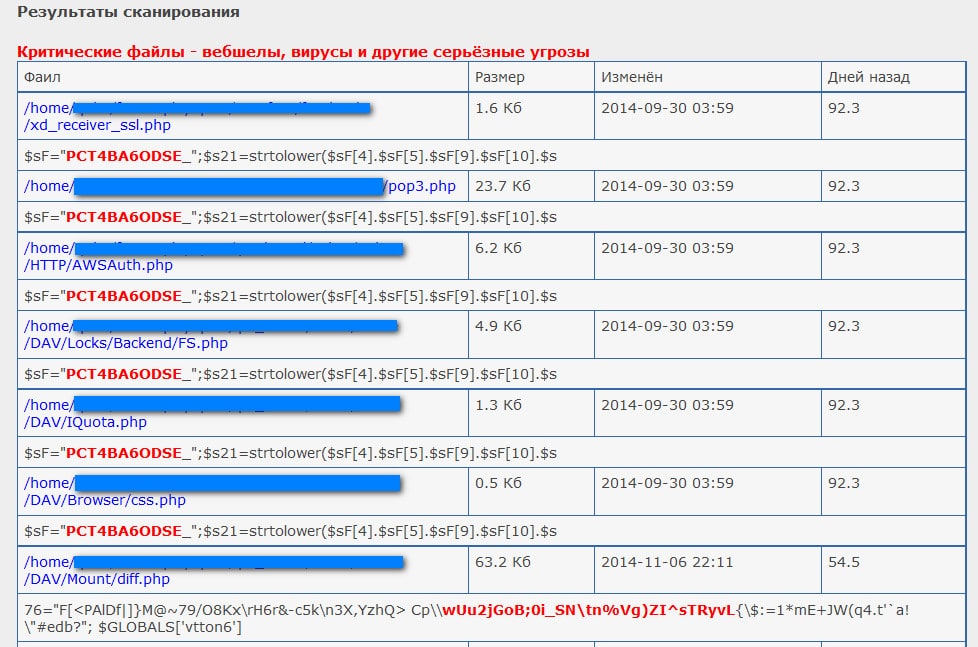
В закрашенном на примере поле указан путь к файлу, в котором был обнаружен код из базы вредоносных сигнатур.
В примере показано несколько файлов, но по факту найдено только две сигнатуры:
1 - PCT4BA6ODSE
2 - wUu2jGoB;0i_SN\tn%Vg)ZI^sTRyvL
Рассмотрим первый вариант.
Откройте WebFTP в новом окне, и в поле путь пропишите путь одного из найденных файлов /home/LOGIN/папки/xd_receiver_ssl.php
Нажмите на файл — открывается файл в текстовом режиме. Сначала визуально ничего подозрительного не видно.
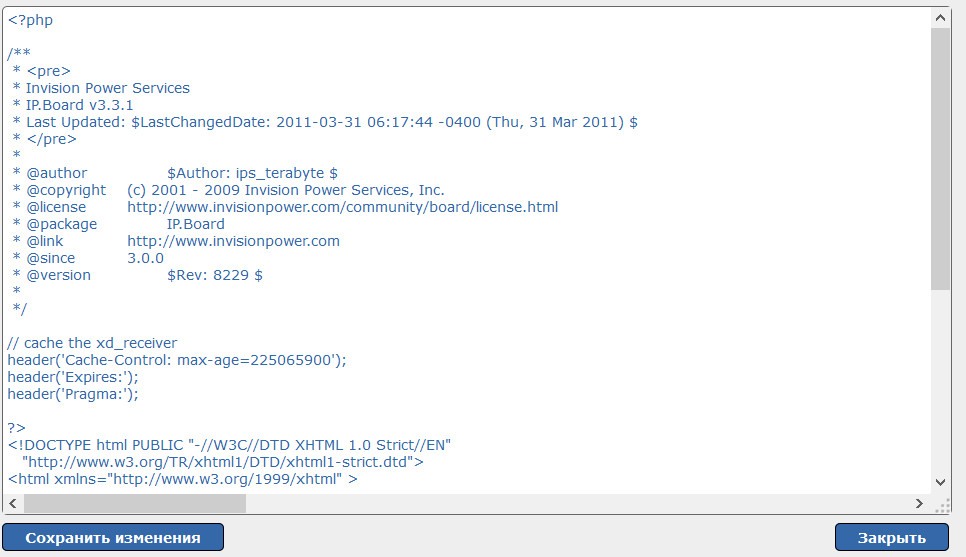
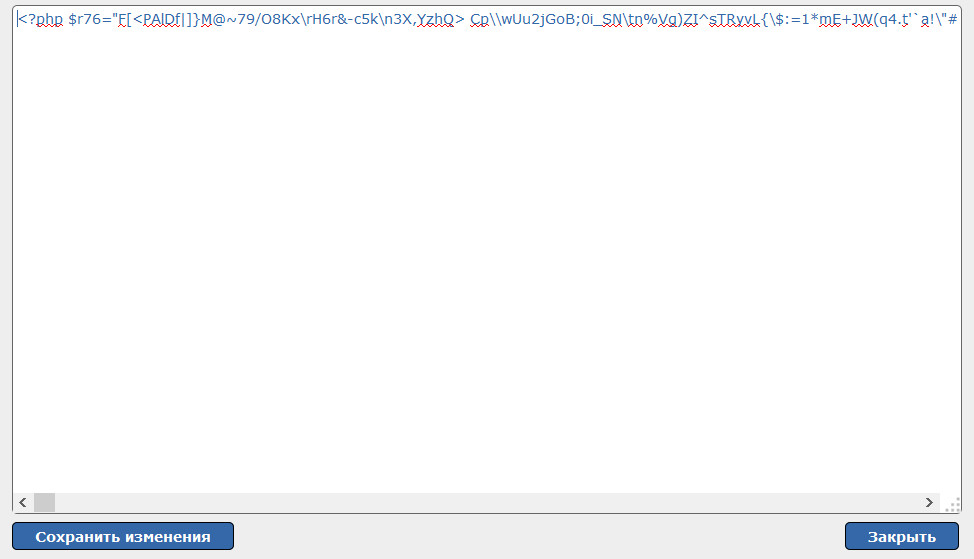
Но если немного промотать скролингом вбок, как сразу увидим вредоносный код:
Удалите вредоносный код и сохраните файл.
Этот пример говорит о том, что вредоносный код был внедрен в нормальный файл от CMS. Этот код нужно удалить из файла, при этом сам файл оставить, либо просто заменить его на исходный.
Необходимо внимательно проверять любой результат сканирования и сверять файлы с исходными, которые от разработчика.
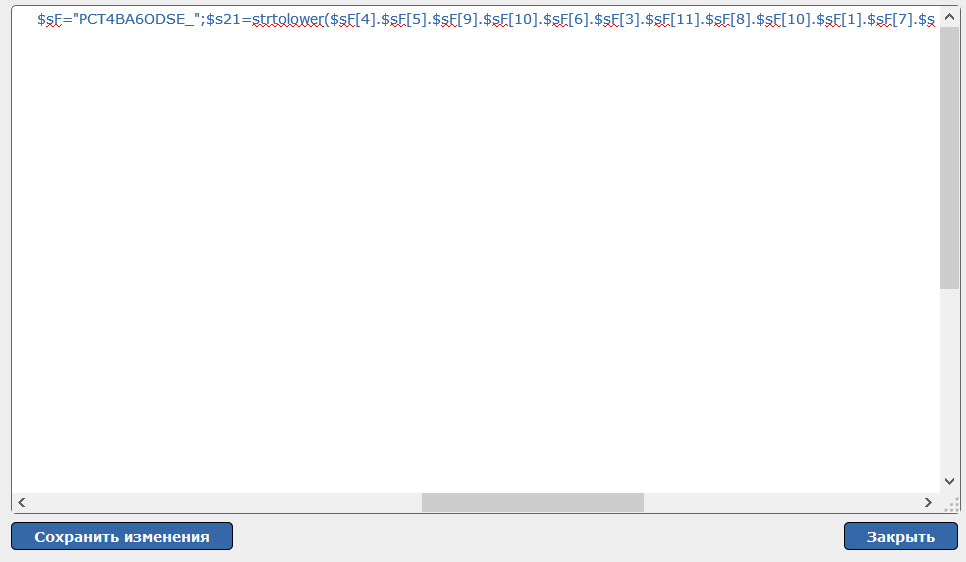
Переходим к варианту номер два:
Через WebFTP откройте файл/home/LOGIN/папки/diff.php:
Мы сразу видим закодированный код. Кода от CMS нет. С вероятностью в 98% этот файл является вредоносным и необходимо удалить весь этот файл. Вполне возможно, именно таким файлом и были заражены остальные.
Таким же образом мы проверяем каждый файл указанный сканером.
Откуда берутся вредоносные файлы?
Как правило, владельцы сайтов не задумываются о безопасности своих сайтов и даже не подозревают, что их сайты могут использоваться как инструмент для заражения вирусами, совершения атак на другие сайты или прочих злых намерений.
В большинстве случаев сайты взламывают через уязвимости в их скриптах.
Как защититься от взломов сайтов?
Если система управления сайта (движок, скрипт) была написана самостоятельно — нужно искать уязвимости и устранять их, в случае же готовых решений cms (wordpress, joomla, dle, drupal и т.д.), необходимо использовать только последнюю, оригинальную и официальную версию скрипта cms от разработчиков.
Внимание!
Не используйте nulled (раскодированные/взломанные) версии cms. Не устанавливайте дополнения, плагины, модули, хаки, темы и прочие добавления от сомнительных, не официальных источников — недобросовестные разработчики дополнений могут внедрять код в свою разработку, позволяющий получать доступ ко всем файлам сайта, что может обернуться большими проблемами для вас.
Важно
Необходимо регулярно обновлять версию cms и всех установленных дополнений, плагинов, расширений до последних версий, так как именно в последних версиях разработчики закрывают многие уязвимости в своём продукте.
Обратите внимание, если вы будете удалять данные файлы или вредоносные коды в них без расследования причин их появления, через некоторое время они снова появяться. Обязательно нужно проверить используемые CMS и/или плагины на наличие обновлений, либо самостоятельно устранить уязвимости в скриптах.